Centos7默认的openssl版本过低,导致无论你怎么配置ssl网站都会一堆漏洞,评价F甚至更低。
漏洞参考这里:https://www.trustasia.com/OpenSSL-CVE-2016-2107-Padding-Oracle
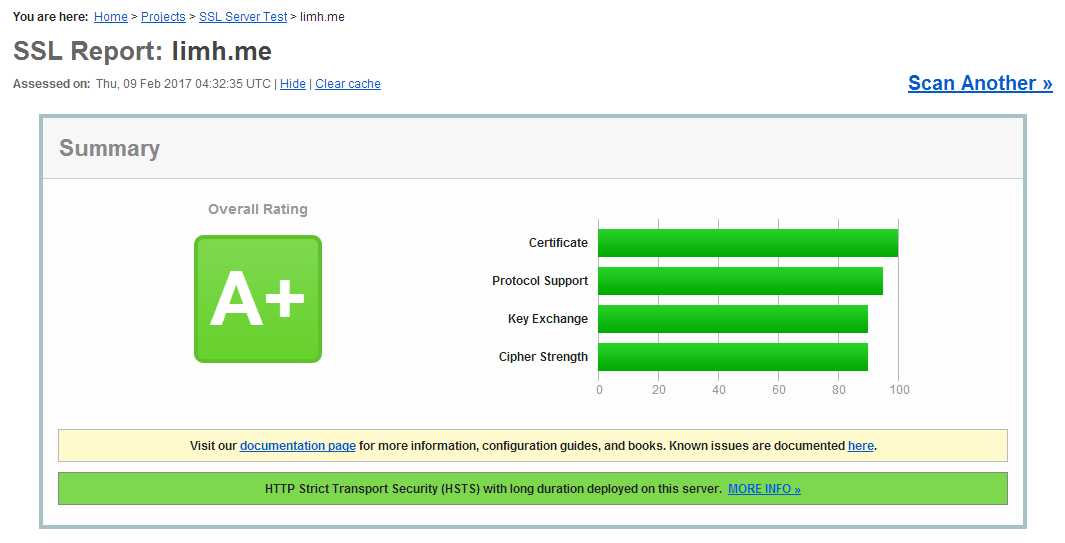
配置完后如图:
测试ssl安全性地址:https://www.ssllabs.com/ssltest/
CentOS 升级 openssl:
1. 安装依赖环境:
yum install pcre-devel zlib unzip git
2. 查看当前 OpenSSL 版本:
openssl version
得到结果:
OpenSSL 1.0.1e-fips 11 Feb 2013
3. 下载 OpenSSL 的最新版:
去官网 https://www.openssl.org/source/ 选择最新的就可以。我这边现在是 1.1.0d
wget https://www.openssl.org/source/openssl-1.1.0c.tar.gz tar -zxvf openssl-1.1.0c.tar.gz
4. 进入目录编译安装:
-
- cd openssl-1.1.0c
-
- ./config --prefix=/usr --openssldir=/etc/ssl --libdir=lib shared zlib-dynamic
-
- make depend
-
- make && make install
如果不能make就说明没有安装gcc
yum install gcc gcc-c++ autoconf automake
如果提示:
zlib.h: No such file or directory
就说明缺少zlib的头文件, 开发包没装
yum install zlib (系统默认已经装上) yum install zlib-devel
5. 拷贝 so 库到指定位置
cp /usr/lib/libssl.so.1.1 /usr/lib64/libssl.so.1.1 cp /usr/lib/libcrypto.so.1.1 /usr/lib64/libcrypto.so.1.1
6. 查看 OpenSSL 最新版本
openssl version
OpenSSL 1.1.0d 26 Jan 2017
nginx 配置,只贴出 SSL 相关,开启http2要求nginx版本1.9以后,一般都是1.10...
需要将配置放到 conf 的 server {} 位置。
首先开启 ssl 和http/2
listen 80; listen 443 ssl http2; server_name limh.me www.limh.me; index index.php index.html index.htm default.php default.htm default.html; root /www/wwwroot/limh.me; #error_page 404/404.html; ssl_certificate key/limh.me/key.csr; ssl_certificate_key key/limh.me/key.key;
生成 dhparam.pem,作用自行百度...
cd /etc/ssl/certs openssl dhparam -out dhparam.pem 4096
配置到 nginx:
ssl_dhparam /etc/ssl/certs/dhparam.pem;
协议和 ciphers 选择,ciphers 的选择比较关键,这个配置中的 ciphers 支持大多数浏览器,但不支持 XP/IE6。
ssl_protocols TLSv1 TLSv1.1 TLSv1.2; ssl_stapling on; ssl_ciphers "ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:AES:CAMELLIA:DES-CBC3-SHA:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!MD5:!PSK:!aECDH:!EDH-DSS-DES-CBC3-SHA:!EDH-RSA-DES-CBC3-SHA:!KRB5-DES-CBC3-SHA"; ssl_prefer_server_ciphers on;
ssl session 配置:
ssl_session_cache shared:SSL:10m; ssl_session_timeout 10m;
HSTS配置,这个对评分影响也比较大,但如果开启这个,需要全部网站都开启HTTPS 。
add_header Strict-Transport-Security "max-age=63072000; includeSubdomains; preload";
完整配置文件:
server {
listen 443 ssl http2;
server_name www.example.com;
ssl on;
ssl_certificate /etc/ssl/certs/你的证书.crt;
ssl_certificate_key /etc/ssl/private/你的密钥.key;
ssl_dhparam /etc/ssl/certs/dhparam.pem;
ssl_session_cache shared:SSL:10m;
ssl_session_timeout 10m;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_stapling on;
ssl_ciphers "ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:AES:CAMELLIA:DES-CBC3-SHA:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!MD5:!PSK:!aECDH:!EDH-DSS-DES-CBC3-SHA:!EDH-RSA-DES-CBC3-SHA:!KRB5-DES-CBC3-SHA";
ssl_prefer_server_ciphers on;
add_header Strict-Transport-Security "max-age=63072000; includeSubdomains; preload";
location / {
# pass
}
}
本教程也适用于Apache和其他类似环境,关于更多有关配置的说明和其他细节,参考:http://www.open-open.com/lib/view/open1430794673710.html
文章评论